
This code takes a property from an untrusted HTTP post named name and uses that as input to a SQL statement. If I use an HTTP POST tool, like Postman, I can test the code:
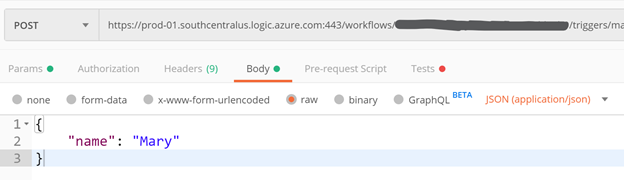
In this example, the name Mary is inserted into the database and the code is working as intended. But if the untrusted input is changed to something like this:
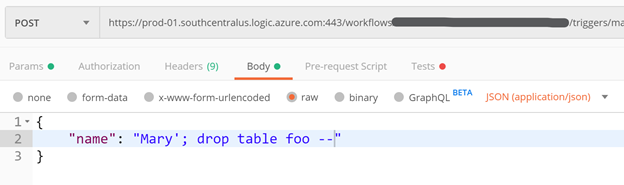
Well, I think you know what happens! Assuming the connection to SQL Server has enough privilege to delete the foo table this code will go ahead and delete the foo table.
Remember, one good definition of a secure system is a system that does what it’s supposed to do and nothing else. In this example, the code can delete a table, and that is far above what was written in the spec!
Most common SQLi attacks are used to exfiltrate data when using SQL select clauses using the classic or 1=1 -- string and the myriad of variants.
The Remedy
The remedy is to use another SQL Server action rather than the Execute a SQL Query action. The SQL Server connector has plenty of other, more constrained actions.
You can also use the Execute Stored Procedure action, as that will use SQL parameters under the hood.
If you must accept untrusted data in order to construct a SQL statement, make sure you use SQL parameters as shown below. Note that using parameterized queries to build SQL statements is as true today as it was well over a decade ago!
Notice how the SQL query has changed to use @name, which is a parameter declared using the formalParameters option. The key is the parameter name and the value is the SQL data type which should match the table definition.
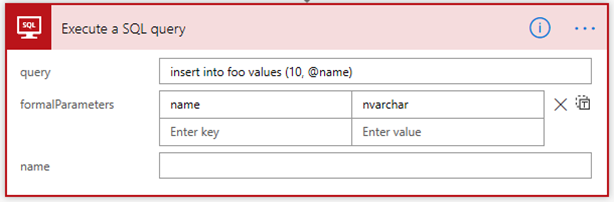
Now the value of this parameter can be set to reference the name dynamic content that came from the HTTP POST request in the actual parameter value below

So there you have it, use SQL parameters! Be careful out there!
I hope that helps, if you have any questions please leave a comment.